Access control and video surveillance integration provide a higher level of security within your organization.
Integrated security systems use access control to authorize and restrict entry while confirming identity via video cameras.
Video surveillance provides reliable visibility into a space while using the same interface as your access control for ease of use.
Unifying the systems (whether two or more are integrated) simplifies operations, improves visibility, creates more control, and provides more in-depth analytics. Instead of trying to navigate independent platforms, administrators of many businesses can view critical information from a single interface and with real-time monitoring.
What is an access control and video surveillance integration?
Traditionally, the security industry has created standalone, proprietary systems. However, the most effective security plans need a product ecosystem that works together.
Integrating access control and video surveillance combines different hardware and software products into a single platform. This enables personnel to view critical information in a single interface.
Typically, we see this as overlayed access control data on a live camera feed. The information that's displayed can include:
- Date and time stamps
- Badge holder’s name
- Badge number/ credential number
- Door or area accessed
- Whether access was granted or denied
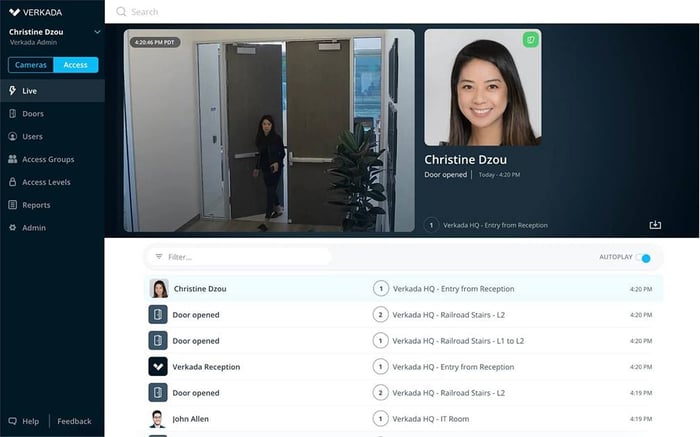
Access control information overlaid on video surveillance footage. Img Source: Verkada
Benefits
Bridging the gap between access control and video surveillance provides various benefits and insight for end-users, building owners, tenants, and guests. Below are some top reasons clients opt for an integrated security approach.
1. Increased Efficiency
Integrating systems streamlines operational efficiencies. When the multiple software and hardware platforms work together seamlessly, they provide a better user experience, and personnel only have one interface to learn and monitor. It also simplifies system updates, training, and daily workflows. Many security vendors now have smartphone apps and sleek website interfaces, simplifying management.

Rhombus security platform.
When you need to investigate an event that's occurred, an integrated system makes it easy. Search by time, date, badge number, name, or location and promptly address the issues.
Alternatively, if your systems aren't integrated, someone has to audit access logs and try to manually match that information with surveillance footage, wasting time and resources. Integrate your access system and software for the best performance.
2. Improved Safety
Systems that work in tandem with each other provide more robust security measures, effectively mitigating risk. By providing visual context for access control events, you can instantly investigate and address situations. Below are some typical applications.

Tailgating detection by Camio.
Tailgating: Identify and address one of the most common security issues the moment it happens.
Loss Prevention: Track individuals through a space and look for suspicious behavior.
Emergency Protocols: Monitor the flow of employees during an evacuation or drill.
Occupancy Management: Track and verify the number of people in a space, a particularly important feature if you need to enforce social distancing due to COVID-19 regulations.
(Check out our on-demand webinar, How Cloud-Based Security Offers Organizations a Safer Reopening.)
3. Real-Time and Remote Monitoring
Depending on your selected platform, integrated access control and surveillance systems could provide real-time and remote monitoring. So, if you have multiple sites, one person can monitor them from a single location. Even if you have one location, your team can view live footage from anywhere on a phone, tablet, or computer and act accordingly.
By viewing the video and access control data simultaneously, rather than linking and reviewing them retroactively, you can search the system and respond to security incidents in real time. Quickly addressing concerns will improve your organization's overall safety and help minimize threats over time.
4. Centralized Data
A centralized system means combining data from multiple sources into a single interface. You can extract meaningful insights and data when all relevant information can be looked at together.
However, integrations aren't limited to access control and video surveillance software. You can also tie in other software to the system.
- Visitor Management Platforms
- Wellness Forms
- Temperature Checks
- Occupancy Sensors
- IoT Devices
- Intelligent Video Monitoring Software
- AI
- And More!

S2 Magic Monitor program.
Adding these additional systems and centralizing all the data provides a more thorough understanding of your space to create a more robust and effective security plan. Integrating these platforms allows you to automatically (without any extra work on your part):
- Identify tailgating hot spots.
- Measure foot traffic and space utilization.
- Restrict access to a space if an individual fails a wellness attestation.
- Receive an alert for suspicious activity.
- Greater access to an area based on occupancy.
- Issue guest/visitor passes and remotely monitor activity.
- Investigate previous incidents with smart search.
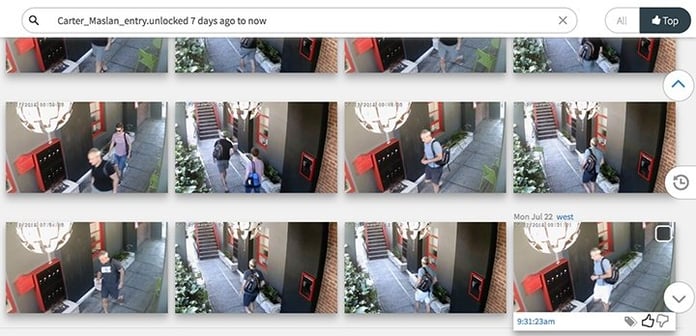
Camio smart search feature.
As incredible and powerful as these integrations are, they aren't necessarily a good fit for every user. Just because you feel like you should integrate the systems for the reasons stated above, you need to ensure that you truly benefit. After all, integrating systems costs money, and the expense must be justified.
Who benefits most from an access control and video surveillance integration:
- Multi-Tenant Buildings
- Large corporate offices or headquarters
- Sensitive areas where security is a top priority
- Sites where thefts/incidents occur regularly
- Organizations looking for additional insights and enhanced security
Who might not benefit from an access control and video surveillance integration:
- Small buildings where strangers would quickly stick out
- Tenants who use biometric access control systems, as these aren’t susceptible to lost/stolen credentials
- Organizations where you don't frequently monitor detailed security records due to a lack of personnel or need
- Those with a very tight budget
It boils down to two questions:
Will integrating access control and surveillance systems increase efficiency?
Will integrating the systems add a layer of security for our organization?
If you answered yes to these questions, you're an excellent candidate and should consider investing in an integrated approach.
Best Practices
When it comes time to embark on your next security project, follow these best practices to ensure your installation and integration go smoothly.
(Related: 9 Workplace Security Best Practices - Are You Jeopardizing Your Business?)
1. Plan Ahead
A traditional project might look like this:
The architect selects the locking hardware.
The security consultant chooses video surveillance.
The building owner picks the access control.
A variety of vendors install each of the systems.
Suddenly, instead of having an ecosystem of security products, you have an array of disconnected platforms. This breakdown in communication and system selection can be costly to rectify.
Since most access control and surveillance systems do not integrate right out of the box, deciding early on what capabilities and integrations your organization needs is vital. Then that functionality must drive the selection of products and installation.
2. Carefully Determine Camera Placement
This likely goes without saying, but make sure all cameras are unobstructed and out of the way. For the best-quality video, a professional may need to survey the site and determine the best placement. Getting an experienced consultant to do this can reduce the number of cameras necessary, increase the amount of covered square footage, and minimize vandalism and tampering.
3. Consider the Cloud
For a good reason, cloud-based access control and video surveillance are trending. Updates are easier, scaling is simpler, and they can be managed remotely. Additionally, storing files in the cloud means no DVRs, NVRs, servers, or hard drives to deal with, and storage plans are often customizable, so you only pay for the storage you need.
4. Don’t Overload Bandwidth or Power Supplies
To minimize downtime, power your access control infrastructure and video surveillance separately. At a minimum, invest in surge protection to reduce interruptions.
Additionally, as higher-resolution cameras become more common, bandwidth consumption must be scrutinized. High-megapixel cameras streaming around the clock can quickly bog down your network. This comes back to planning; make sure you know what functionality you need and let that guide your system selection.
Access control and video surveillance integration provide a layered and more robust security system. On top of that, daily users can easily monitor and manage the system while gaining detailed insights into the space, keeping everyone in the organization safe.
This increase in efficiency and security justifies the cost of integration if you have an experienced technology partner guiding the process.
Our team of security professionals is here to help you select, install, and integrate your access control and surveillance systems. If you have any questions or want to discuss an upcoming project. We invite you to schedule a free consultation. Contact Us today.
To learn more about pricing, download our Access Control & Surveillance Purchasing Guidebook below.
Editor's Note: This post was originally published in September 2020 and has been updated for freshness, accuracy, and comprehensiveness.



Leave a Comment